Threat TV
Top Viewed Videos
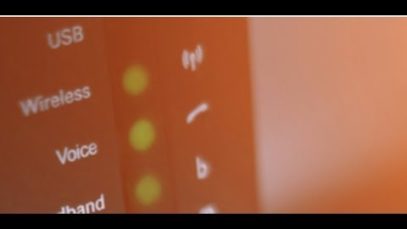
Is Your Router Being Exploited? | Malware Monday!
Did you know a cyber attacker can utilize one of those many routers you use every day to further their agenda? Hackers could easily be using your router to conduct many types of malicious attacks, like sending harmful spam to unsuspecting victims or using phishing websites to steal passwords. Cyber attackers like the idea of […]
New Malware A Warning For War? | Malware Monday!
Recently discovered malware in Ukraine is called “Pterodo,” a new version of something older that gives cyber attackers illicit access to computer systems. This newly discovered Pterodo is a modified version of the previously discovered Pterodo. It gets information about how the computer systems are set up, sends the information to the cyber attacker’s own […]
How Trickbot Steals Your Bank Password | Malware Monday!
Criminals can use databases full of credit card data and online banking credentials to make huge amounts of money through identity and financial fraud. To find out how TrickBot operates and how to prevent it, go to TheThreatReport.com right now to read the full story. (Visited 499 times, 1 visits today)
Ransomware For Sale On The Dark Web Is A Killer Bargain For Criminals
Researchers at cybersecurity firm Sixgill have discovered a seller on a darknet market is offering a huge collection of ransomware for about $750. That’s a great value for cyber attackers because they can make so much more money from getting their victims to pay their ransoms, possibly even millions of dollars! Sixgill’s Gilad Israeli says, […]
Insidious Text Messages | Malware Monday!
This malware Monday focuses on insidious text massages you may be receiving! They tend to be texts claiming you need an app to listen to voicemails or do other everyday tasks on your smartphone. Do not ever click these links or download the apps as they most likely will place malware on your device. Specifically […]
4 Key Cybersecurity Themes to Remember | The Threat Report News
Every October since 2004, the U.S. Department of Homeland Security and the National Cyber Security Alliance have co-sponsored National Cybersecurity Awareness Month. This year’s overarching theme, “Our Shared Responsibility” is kind of like the “See something, say something” motto that’s often heard in other security venues, meaning cybersecurity is not just the responsibility of a […]
Top Liked Videos
VIEW MOREWays A Cyberattack Can Literally Kill You | The Threat Report News
While it’s true cybersecurity providers and governing bodies do everything within their power to keep data safe, but the biggest question is: Are we doing enough to keep people—real, living people—alive and safe? Full Story: https://bit.ly/2DfOCgd (Visited 360 times, 1 visits today)
The Threat of Cyberattacks On 911 Services | The Threat Report News
Cyber attacks On 911 Services have increased in recent times. Have you ever stopped to consider what you might do if a critical call for help was denied because you could not connect to 911? This is a reality thanks to attacks known as a Telephony Denial-Of-Service. The attacker’s strategy is to overload 911 phone […]
The Nightmare of 2018’s Data Breaches | The Threat Report News
One of the biggest hacks of 2018 saw Facebook get hit with a breach of 50 million user accounts. Facebook was in good company however as 2018 also saw T-Mobile, British Airways, Google and most recently Marriott experience major data breaches. 2018 has seen consumer worry spike drastically about having their data jeopardized online. To […]
Protect Your Money From Scams | The Threat Report News
Global losses due to fraudulent credit card, debit card, and mobile payment transactions reached $22.8 billion in 2016, according to recent data from the trade publication Nilson Report. You will never be able to fully avoid credit card theft unless you stopped using them altogether, but there are precautions you can take. Read Full Story: […]
Northeastern Ontario Hospitals Hacking Incident, The Aftermath
Twenty-four Northeastern Ontario hospitals were victims of the latest cyber attack with the use of zero-day exploits. Zero-day exploits are unknown security bugs in software that are actively exploited by hackers in order to gain control, launch malware or open other vulnerabilities in the target system. To read full article: https://www.thethreatreport.com/24-northeastern-ontario-hospital-hacking-incident-the-aftermath/ (Visited 447 times, 1 visits […]
(Visited 4211 times, 1 visits today)